Network Design and Structure
Title: Network Design – When implementing a network in an organisation, there are some design issues that must be considered before implementation. The requirements of the network must be clearly defined and all the network components to be used have to be clearly defined. Some of the considerations are discussed below.
Network Design and Network Architecture
Network architecture is the infrastructure consisting of software, transmission equipment, and communication protocols define the structural and logical layout of a computer network. The mode of transmission of a network can be wired or wireless depending on the requirements in an organisation. There are various types of networks that can be applied in an organisation depending on the network size. Local area network (LAN) refers to network in a small geographical area, Metropolitan area network (MAN) refers to network in a city, and wide area network (WAN) refers to network that is spread geographically in a wide area. Among the three types of network, the company would implement LAN since it is only covering a small geographical area.
Transmission Media
The transmission medium of a network can be wired or wireless. Wired medium involve use of coaxial cables or fiber-optic cables while wireless media involves wireless transmission of data. Depending on the bandwidth, throughput and goodput we are able to determine the best medium of transmission. Fiber optic cables have low signal loss since they avoid collision, and they are efficient in data transfer in high traffic networks. Coaxial cables are less expensive compared with fiber optic cables, but they have high signal loss caused by collisions. Wireless transmission is efficient in local area network where there are few computers.
Network Design Management Method
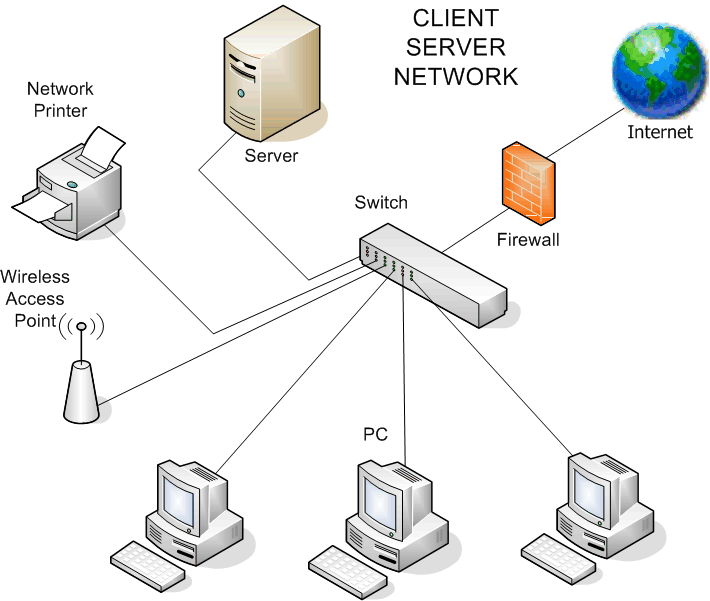
The management method of a network can be either peer to peer or client-server. Peer to peer is where there is communication between several computers without a central computer. Client-server is where each client is independent and a central server provides services to the clients. In a peer to peer network, many computers can share a single application installed in one computer. In a client-server, they are designed to support large number of clients where the clients do not share resources. The client-server model security is enhanced because security is handled by the server. It is also easy to upgrade a client server model to meet new requirements in an organisation.
Figure 1, a client server model
Network Topology
Network topology is divided into physical and logical topology. Physical topology refers to the way in which computers and other devices are connected. Logical topology describes the layout of data transmission in a network. Bus, ring, star and mesh topologies are the main types of topologies. Bus topology is a where all devices are connected with a single cable. The topology works for small networks, but it is slow and collisions are common. Ring topology is where the cable runs around where each node is connected to each other. There are fewer collisions compared with a bus topology. A token ring is used to avoid collision. In a star topology, all the devices are connected to a central hub. There is a central management making it is faster in upgrading, but failure of the central hub brings down the entire network. Mesh topology connects all the devices to each other for fault tolerance and redundancy to improve performance.
Network Design Security Requirements
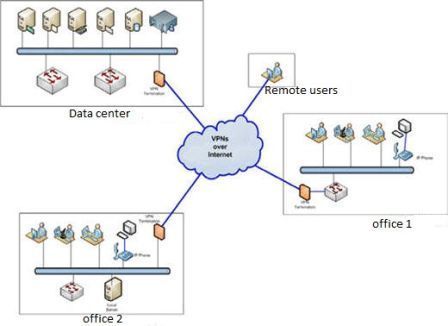
Networks are frequently attacked by hackers and other malicious people. This makes security one of the key considerations when designing a network. To reduce the number of attacks on computer networks, the network should have firewalls, intrusion detection systems, VPN, and DMZ. These measures reduce the threat and detect malicious people in the network.
Scalability
This refers to the ability of the network to grow. The network should be scalable enough to cater for growth in the network infrastructure.
Network Address Translation (NAT)
This is a design consideration where many computers in a private network access the network using one public IP address. This is a measure to enhance security in a network.
Figure 2, Network architecture
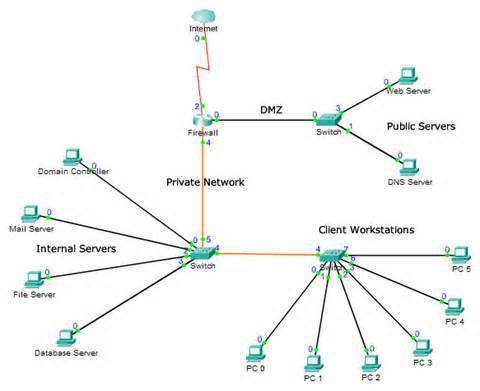
Figure 3, Showing how VPN is implemented
OSI Reference Model in Network Design
The OSI model has seven layers as highlighted in the diagram. The communication system is sub-dived into layers where each layer sends service requests to the layer below it and receives service requests from the layer above it (FitzGerald & Dennis, 2009).
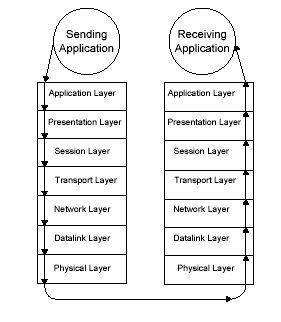
Layer 1: Physical Layer
Physical layer refers to the hardware and all network devices used in the network. The layer defines the physical devices and the transmission medium. The layer receives service requests of the data-link layer and performs encoding and decoding of data in signals. Protocols in this layer include CSMA/CD, and Ethernet (Liu, 2009).
Layer 2: Data-Link Layer
Data-link layer receives service requests of the network layer and sends service requests to the physical layer. The main function of the data-link layer is to provide reliable delivery of data across networks. Other functions performed by the layer include framing, flow and error control, and error detection and correction. There are two sub layers of the data-link layer; media access control layer, and logical link control layer. Media access control performs frame parsing, data encapsulation and frame assembly. Logical link control is responsible for error checking, flow control and packet synchronisation. Protocols in this layer include; X 25, frame relay and ATM.
Layer 3: Network Layer
Network layer is responsible for managing all the network connections, network congestions, and packet routing between a source and destination. The layer receives service requests of the transport layer and sends service requests to the data-link layer. The main protocols in this layer are IP, ICMP, and IGMP.
Layer 4: Transport Layer
The main purpose of this layer is to provide reliable data delivery which is error free by performing error detection and correction. The layer ensures that there is no loss of data, and data is received as it was sent. The layer provides either connection-less or connection oriented service. There are two protocols in this layer: UDP and TCP.
|
TCP
|
UDP
|
Layer 5: Session Layer
The main purpose of this layer is to establish and terminate sessions. The layer sets up and terminates connection between two or more processes. It also manages communication between hosts. If there is login or password validation, this layer is responsible for the validation process. Check-pointing mechanism is also provided by this layer. If an error occurs, re-transmission of data occurs from the last check-point. Protocols in this layer include; RIP, SOCKS, and SAP.
Layer 6: Presentation Layer
This layer is responsible for data manipulation, data compression and decompression, and manages how data is presented. The layer receives service requests of the application layer and sends service requests to the session layer. The layer is concerned with the syntax and semantics of the data in transmission. Data encryption and decryption (cryptography) is used to provide security in this layer. Protocols involved in this layer include; ASCII, EBCDIC, MIDI, MPEG, and JPEG.
Layer 7: Application Layer
This layer provides interaction with the end user and provides services such as file and email transfers. The layer sends service requests to the presentation layer. It has several protocols used in communication; FTP, HTTP, SMTP, DNS, TFTP, NFS, and TELNET.
Network Protocols
- Ethernet – provides transfer of information on Ethernet cable between physical locations
- Serial Line Internet Protocol (SLIP) – used for data encapsulation in serial lines.
- Point to point protocol (PPP) – this is an improvement of SLIP, performs data encapsulation of serial lines.
- Internet Protocol (IP) – provides routing, fragmentation and assembly of packets.
- Internet Control Management protocol (ICMP) – help manage errors while sending packets and data between computers.
- Address resolution protocol (ARP) – provides a physical address given an IP address.
- Transport control protocol (TCP) – provides connection oriented and reliable delivery of packets.
- User datagram protocol (UDP) – provides connection-less oriented service and unreliable delivery of packets.
- Domain name service (DNS) – provides a domain name related to a given IP address.
- Dynamic host configuration protocol (DHCP) – used in the management and control of IP addresses in a given network.
- Internet group management protocol (IGMP) – support multi-casting.
- Simple network management protocol (SNMP) – manages all network elements based on data sent and received.
- Routing information protocol (RIP) – routers use RIP to exchange routing information in an internetwork.
- File transfer protocol (FTP) – standard protocol for transferring files between hosts over a TCP based network.
- Simple mail transfer protocol (SMTP) – standard protocol for transferring mails between two servers.
- Hypertext transfer protocol (HTTP) – standard protocol for transferring documents over the World Wide Web.
- Telnet – a protocol for accessing remote computers.
Figure 5 shows the TCP/IP architecture
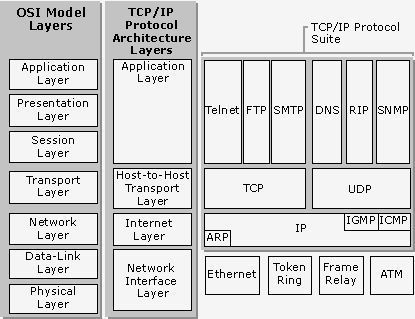
Layer 1: Network Access Layer
This layer is responsible for placing TCP/IP packet into the medium and receiving the packets off the medium. This layer control hardware and network devices used in the network. Network access layer combines the physical and data-link layer of the OSI model.
Layer 2: Internet Layer
It functions as the network layer in the OSI model. The layer performs routing, addressing and packet addressing in the network (Donahoo & Calvert, 2009).
Layer 3: Transport Layer
The layer has the same functions as the transport layer in the OSI model. The main function of this layer is to provide reliable data delivery which is error free. The layer receives service requests of the application layer and sends service requests to the internet layer.
Layer 4: Application Layer
This is the layer that has applications that perform functions to the user. It combines the application, presentation and session layers of the OSI model.
TCP/IP Commands Used To Troubleshoot Network Problems
There are many TCP/IP commands that can be used to show that there is a break in communication. The commands are: PING, TRACERT, ARP, IPCONFIG, NETSTAT, ROUTE, HOSTNAME, NBSTAT, and NETSH.
Hostname is used to display and show the host name of the computer
Arp is used for editing and viewing of ARP cache.
Ping is used to send ICMP echo to test the reachability of a network
Event viewer shows all the records of errors and events.
References
Donahoo, M. J., & Calvert, K. L. (2009). TCP/IP sockets in C: Practical guide for programmers. Amsterdam: Morgan Kaufmann.
Fall, K. R., & Stevens, W. R. (2012). TCP/IP illustrated. Upper Saddle River, NJ: Addison-Wesley.
FitzGerald, J., & Dennis, A. (2009). Business Data Communications and Network Design. Hoboken, NJ: John Wiley.
Leiden, C., & Wilensky, M. (2009). TCP – IP. Hoboken: For Dummies
Liu, D. (2009). Next generation SSH2 Network Design and Implementation: Securing data in motion. Burlington, MA: Syngress Pub.
Odom, W. (2004). Computer networking first-step. Indianapolis, Ind: Cisco.
Ouellet, E., Padjen, R., Pfund, A., Fuller, R., & Blankenship, T. (2002). Building a Cisco Wireless LAN and Network Design. Rockland, MA: Syngress Pub.
View More Computing Dissertations Here
If you enjoyed reading this post on Network Design and Structure, I would be very grateful if you could help spread this knowledge by emailing this post to a friend, or sharing it on Twitter or Facebook. Thank you.
